Supply chain cyber security policy (standard)
This is a standard-length supplier cyber security policy designed to help businesses to create contractually enforceable obligations on suppliers with respect to cyber security.
This flexible template can be edited either to focus on specific, identified risks, or to apply a general benchmark across a supplier's systems.
Before or while editing the policy, you should establish what the relevant risks are, your general approach to those risks and the resources you propose to invest in mitigating the risks.
Detailed guidance notes are included to help you when editing this document.
In addition to the provisions in this standard version of the policy, the premium version includes provisions covering: (i) evidential requirements and auditing; (ii) detecting breaches; (iii) responding to breaches; and (iv) system and policy reviews and updates.
This policy was created and is maintained by Emma Osborn of OCSRC (https://www.ocsrc.co.uk) in collaboration with Docular.
Supply chain cyber security policy (standard) contents
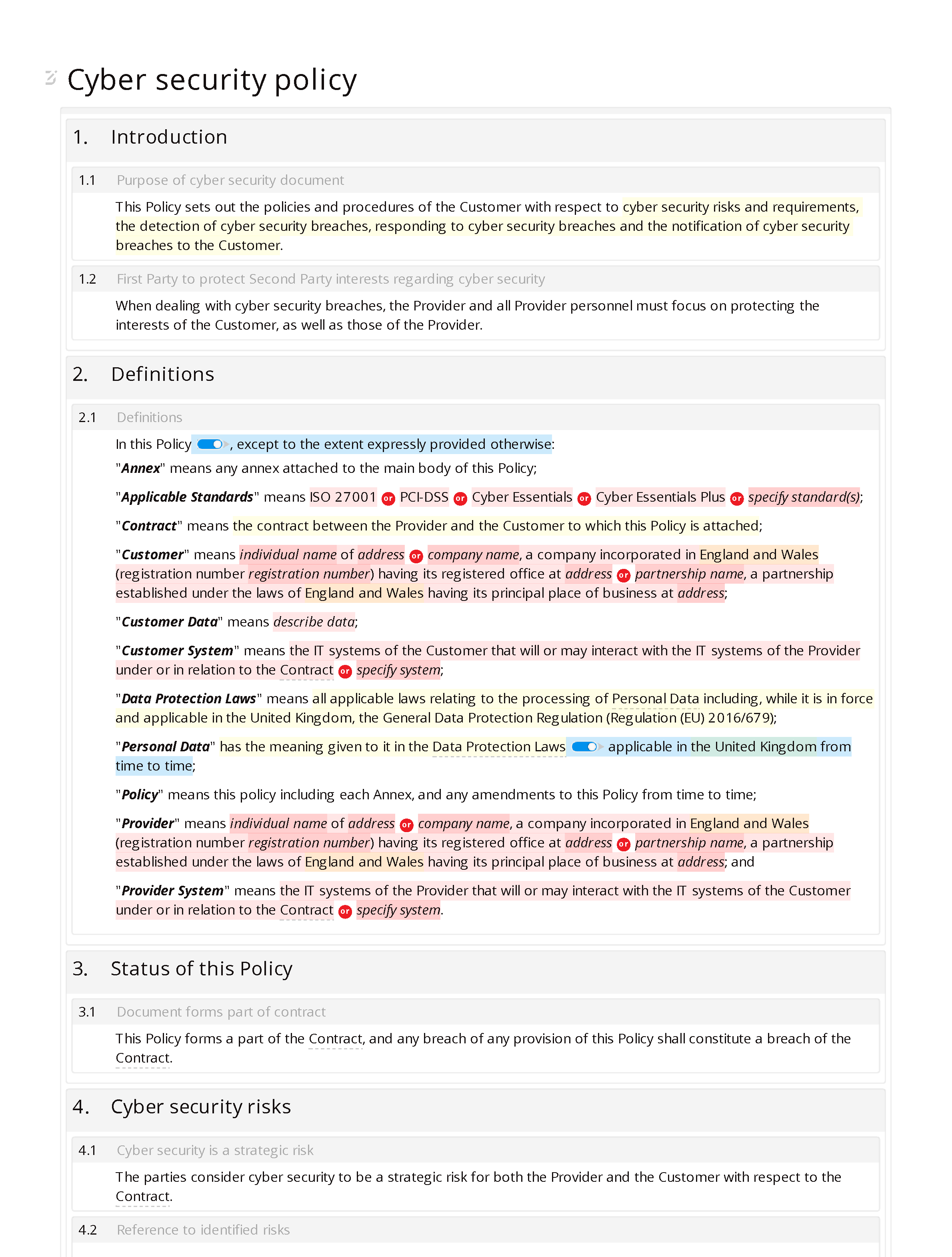
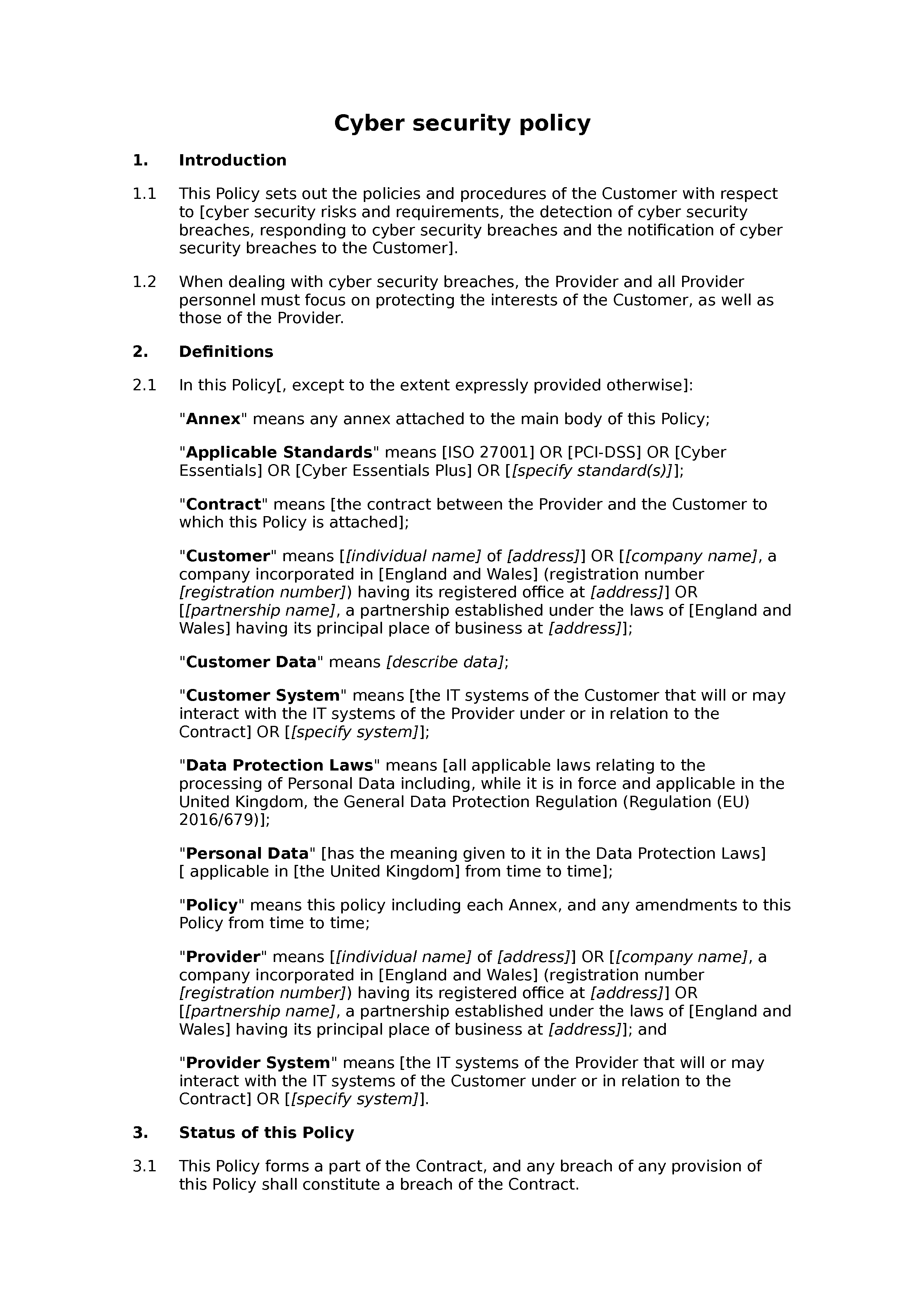
- Introduction: purpose of cyber security document; Providerto protectCustomerinterests regarding cyber security.
- Definitions: definitions.
- Status of this Policy: document forms part of contract.
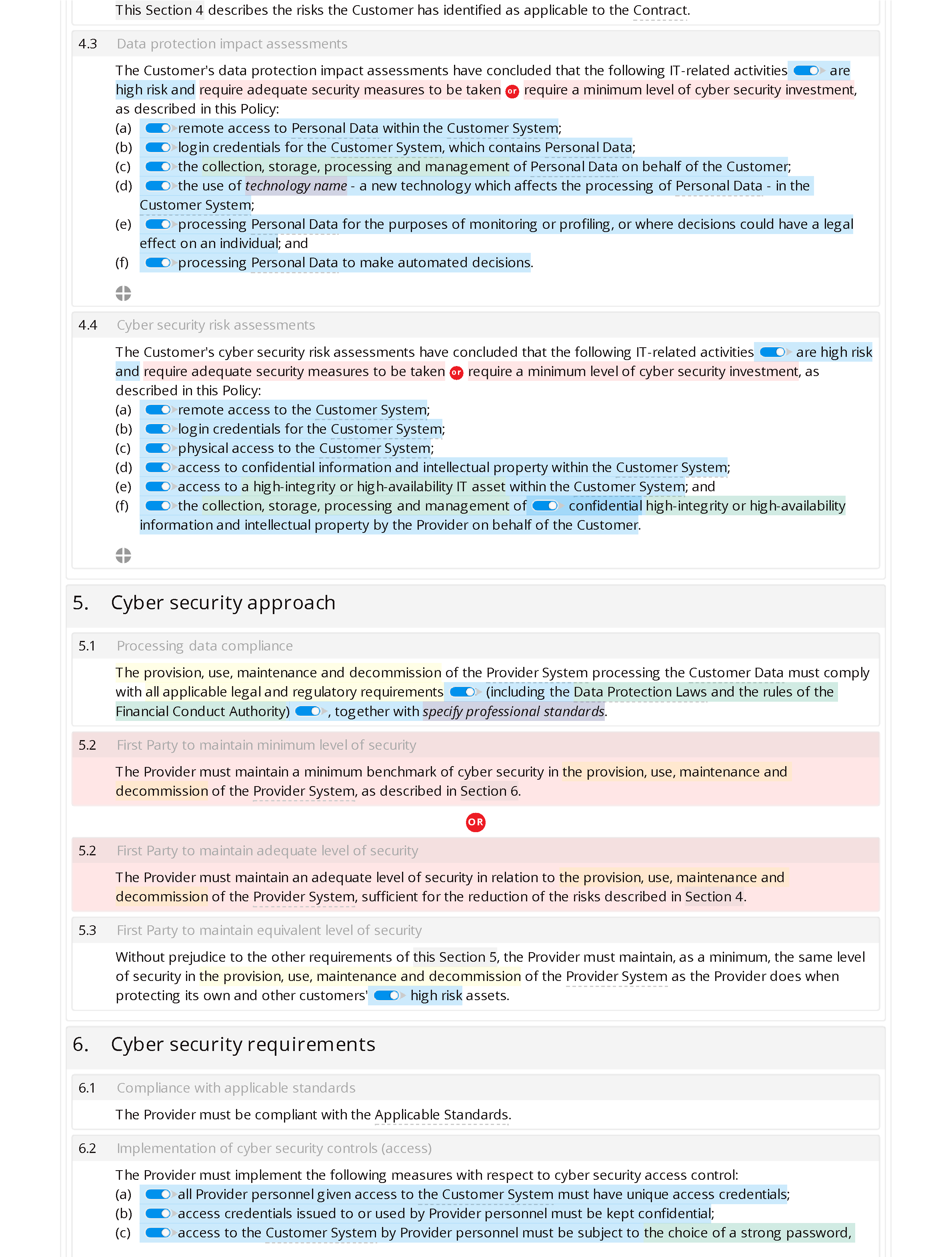
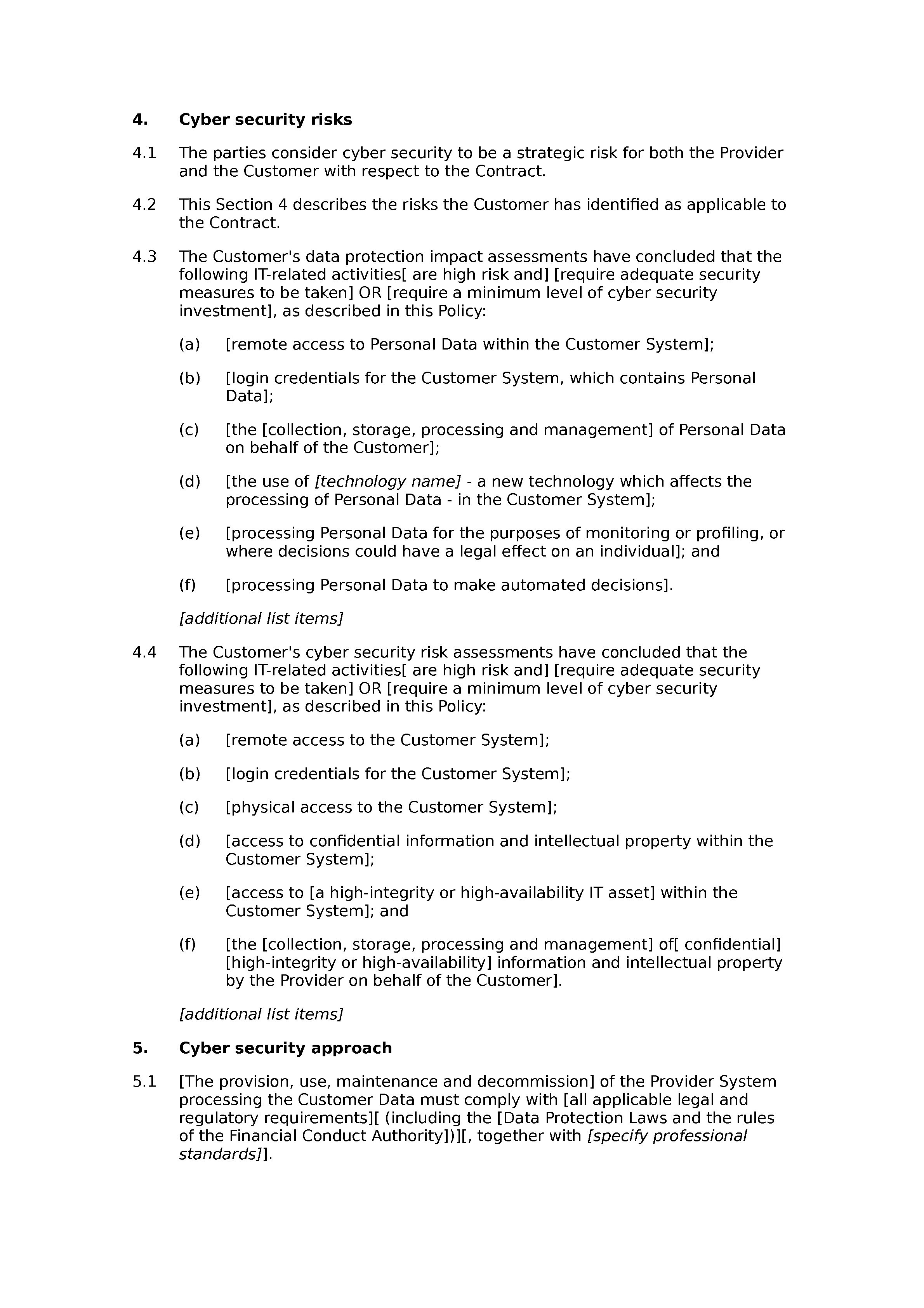
- Cyber security risks: cyber security is a strategic risk; reference to identified risks; Data protection impact assessments; cyber security risk assessments.
- Cyber security approach: processing data compliance; Providerto maintain minimum level of security ;Providerto maintain adequate level of security;Providerto maintain equivalent level of security.
- Cyber security requirements: compliance with applicable standards; implementation of cyber security controls (access); cyber security training requirements; implementation of technical controls.
- Actions upon termination: managing termination of contract; provision of data on contract termination ; deletion of Customerdata ; provision of a record of data retained by the other party; access credentials revoked; requirements remaining in force.
ANNEX 1 (EVIDENCE REQUIRED OF COMPLIANCE)
- List of evidence of compliance with cyber security policy.
ANNEX 2 (ADEQUATE ENCRYPTION STANDARDS)
- List of adequate encryption standards.